Defense in-Depth and Attacks
About Course
The course begins with an examination of the foundations of information assurance, looking at how security threats affect confidentiality, integrity, and availability. From there, it delves into identity and access management (IAM), discussing modern authentication methods and password security, particularly as they relate to cloud computing. IAM is emphasized as a key security perimeter in cloud environments.
The focus then shifts to modern security controls, including frameworks such as the Center for Internet Security (CIS) Controls, the NIST Cybersecurity Framework, and the MITRE ATT&CK knowledge base. These help protect against contemporary threats.
The course also explores mobile device security, highlighting the benefits and risks of mobile technology. Topics include Bring Your Own Device (BYOD) and Mobile Device Management (MDM), offering a comprehensive understanding of mobile technology’s impact on security.
Course Content
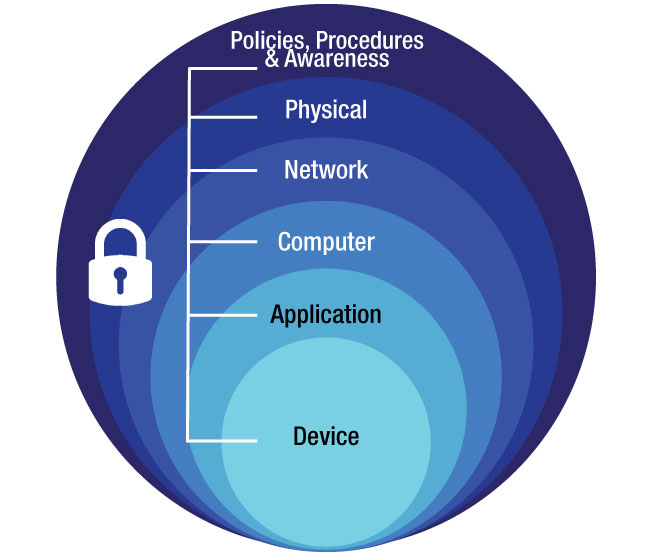
Introduction Defense-in-Depth and Attacks
-
Introduction
Defense-in-Depth
Access Control and Password Management
Security Policies
Critical Security Controls
Malicious Code and Exploit Mitigations
Advanced Persistent Threat
Student Ratings & Reviews
